Keep Your Virtual Meetings Secure with Token Authentication
For many of us, virtual meetings have become a cornerstone of our daily lives. We use them to connect with colleagues, friends and family. Keeping your online meetings secure should be at the top of your priority list.
Cybersecurity threats are everywhere. Hacking, phishing, and data breaches are real risks. The results of these attacks could be devastating for your personal life or business.
This is where token-based authentication can help. We will explore the benefits of securing your online meetings with tokens and how they can help you maintain the highest levels of online meeting security.
Table of Contents
- What are tokens?
- Benefits of securing your online meetings with tokens
- Implementing token-based authentication
- How Digital Samba Rest API leverages tokens
- JWTs for secure token-based authentication
- Conclusion
Whether you use video meetings for personal or business purposes, this article will help you keep your meetings locked and secure from unwanted attacks and intruders.
What are tokens?
To put it simply, tokens are little pieces of data that authenticate a user's identity and grant them access to resources or services. Tokens are commonly used in web applications to manage user sessions and provide secure communications between the client and server.

Tokens function by generating a unique string of characters that are used to authenticate a user's identity. They are considered far more secure than traditional username/password authentication methods. A server typically generates tokens and sends them to clients as a JSON Web Token (JWT).
When clients need to access a protected resource or service, they present their token to the server. The server then grants access if the security criteria are met. Within the context of online meetings, tokens are used to ensure that only authorised users can access a meeting.
Benefits of securing your online meetings with tokens
There are several major benefits to securing your online meetings using tokens. Here are some of the most critical:
Enhanced security
Tokens give your online meetings an extra layer of security. They drastically reduce the risk of unauthorised invaders and help you ensure that only legitimate participants can gain access.
Simplified management
Tokens can be managed centrally and easily revoked or expired if necessary. This simplifies managing online meetings and reduces the risk of unwanted attendees accessing your meetings.
Customisable access
Tokens can be configured to grant different access tiers to different participants. For example, you can use tokens to grant attendees "view only" access rights or "screen sharing" rights.
Improved accountability
You can use tokens to track exactly who is accessing your meetings and when. This gives your organisation a way to monitor meeting attendance and ensure that participants comply with your meeting compliance requirements.

Integrate secure video conferencing into your product
Contact our sales team now!
Implementing token-based authentication
You've learned about the benefits of token-based authentication. But how can you implement it into your online meetings?
Choose a token type
Generate tokens
Secure token storage
Token authentication
Token access control

How Digital Samba Rest API leverages tokens
The Digital Samba REST API uses tokens to secure virtual meetings. Each user is assigned a token that validates their identity when they request access to an online meeting room.
As mentioned above, the API uses JSON Web Tokens (JWT) open standard because it presents the most effective way of keeping your online meetings secure. JWTs are signed or encrypted to securely transfer payload or ensure authorization between parties. To sign JWTs, we’re using the HMAC algorithm (HS256).
A sample JWT token looks like this:
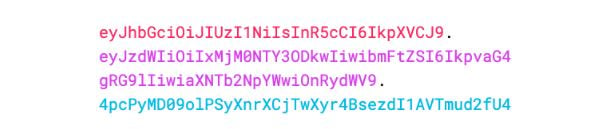
It contains three base64 encoded string components: Header (containing the signing algorithm), Payload (actual data we’re signing), and Signature (signed combination of header and payload), separated by dots. This helps confirm the validity of the token. More on JWTs in the coming section.
The REST API enables developers to set numerous token properties like username, role, and avatar. Explore the full list of token properties here. We highly recommend that developers set a room id (rd) to ensure that the token is only used for the intended video conference. Also, setting other conditions, such as a token validity period through token expiration time (exp) and not-before (nbf) ensures that the token is only valid for the duration of the video conference.
For private meeting rooms, we’ve made tokens compulsory. No one can enter the meeting room without a token. For public rooms, where everyone who knows the URL can enter the meeting room, tokens are needed only if you have more than one role and need to specify with which role the user should enter. Public rooms are less secure than private rooms.
To create and sign a token, you need a developer key and team Id from the Digital Samba dashboard. Use the following JAVA sample code snippet to create your token and sign it using the HMAC algorithm.
String developerKey = "YOUR_DEVELOPER_KEY_FROM_THE_DASHBOARD";
String teamId = "YOUR_TEAM_ID_FROM_THE_DASHBOARD";
String roomId = "YOUR_ROOM_ID";
String username = "John Smith";
Algorithm algorithm = Algorithm.HMAC256(developerKey);
String token = JWT.create()
.withClaim("td", teamId)
.withClaim("rd", roomId)
.withClaim("u", username)
//.withClaim("ud", "ABC1234567254435")
//.withClaim("role", "moderator")
//.withIssuedAt(new Date())
//.withNotBefore(new Date(System.currentTimeMillis() + 3600000))
//.withExpiresAt(new Date(System.currentTimeMillis() + (3600000 * 2)))
.sign(algorithm);
Explore our complete REST API documentation and check out the tokens section for more details.
JWTs for secure token-based authentication
When it comes to securing your online meetings with tokens, The JSON Web Token (JWT) is one of the most powerful weapons in your arsenal. These tokens are a popular tool for secure token-based authentication, allowing users to access your application or API securely and efficiently.
JWTs are "self-contained" ways of securely transmitting information between parties. They are digitally signed and contain payloads of information that can be verified and trusted. Users can log into your application and receive a JWT that they can use for subsequent login requests. This means the user doesn't have to keep inputting login credentials, saving time and reducing the chance of sensitive information being intercepted by third parties.
JWT-based token authentication can help you prevent common attacks like cross-site scripting (XSS) and cross-site request forgery (CSRF)
JWTs are signed using a secret key that renders the token invalid in the event of tampering.
To implement JWT-based authentication, you must set up a server to generate and sign your JWT tokens. You'll also need to integrate JWT verification into your application so incoming requests can be authorised based on the JWT payload.
Using JWTs for secure token-based authentication is an extremely powerful method of securing your online meetings. They drastically reduce the risk of unauthorised access and help you protect sensitive information. Securing your meetings with JWTs will help ensure your meetings are a productive and secure environment for all participants.
Overall, using JWTs for secure token-based authentication can be a powerful way to increase the security and efficiency of your online meetings. By reducing the risk of unauthorised access and protecting sensitive information, you can ensure that your meetings are productive and secure for all participants.
Conclusion
Securing your online meetings with tokens is a powerful means of protecting your data and guaranteeing your participants' privacy. It offers massive advantages compared to traditional authentication methods, including enhanced security, ease of use and scalability. Always follow best practices when implementing token-based security. These include setting appropriate expiration times and keeping all tokens confidential. Implementing token-based security will help you provide a better user experience and ensure the safety of your users' data.
Share this
You May Also Like
These Related Stories
Introducing the new Digital Samba Whiteboard: A Game-changer in Video Conferencing

Introducing Cloud Recordings in Digital Samba Embedded



